Should a contract developer pay for their own components?
I’ve been off blogging on the official Embarcadero blog here: https://blogs.embarcadero.com/author/ianbarker/
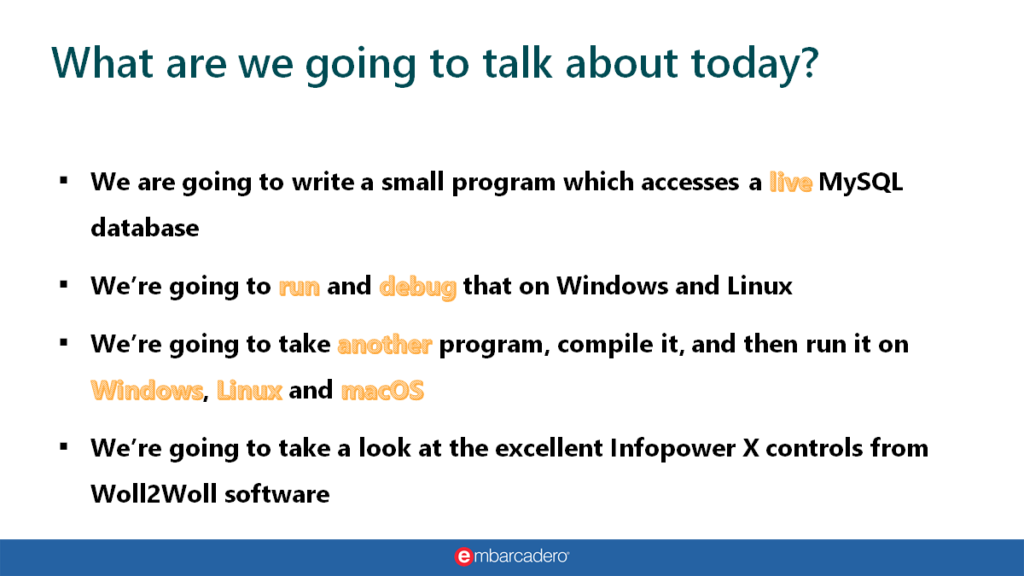
I’ve also been either occasionally guesting or moderating the TCoffeeAndCode webinar series. You can see the latest video below and subscribe to the series here: https://embt.co/3uyNUkg
I really must learn to talk less and listen more.
Should a contract developer be expected to pay for their own components?
I just had slightly painful conversation with a customer who was questioning why they should pay for the purchase of a set of Delphi custom components in order for a contract programmer (not me) to carry out some work for them. The customer’s argument is “it’s like expecting a plumber to get you to buy their screwdriver”. The person chose a firebrand of an analogy there: notwithstanding the fact that in most Western cultures plumbers are horrendously expensive, have call-out fees and hourly rates which put some lawyers to shame and often expect you to sit with a water leak drowning out your house until they are available, it’s also very poor when this particular contractor being discussed is actually from what is often referred to as “a third-world” country.
Globalization is not homogeneous
This particular out-sourced software developer contractor is being paid an hourly rate that is less than the company’s least qualified office staff. The price of the components I was discussing with the company is the same whether the contractor is living in Silicon Valley or a tent in the Sahara desert. The wages of the contractor are reasonable for their culture and represent what he considers to be fair pay for fair work when compared to the cost of living in their home country. But the cost of the component set is almost beyond his reach financially. Welcome to the disparity of globalization. He’s ‘cheap’ in terms of labor costs but the components we are asking him to use have no cost-of-living benefit since they are made in the fluffy environs of a first-world company with corresponding taxation and labor charges of their own, so they set the price to cover those expenses and to make a profit fit for their average standard of living in their country, not the contractor’s more modest financial needs.
What answer can you give to a company who wants the contractor to pay for the third-party components?
The company need the contractor to use a specific set of components which he doesn’t have; which are not particularly common but are vital to the aim of the development and have no credible, cheaper alternative. They have a couple of choices: they can find a contractor already using the components and pay the more expensive going rate for their time, they can get the contractor to pay for them and reimburse him – which his cash-flow might not allow, or they can buy them for him.
Here’s my explanation to the non-technical gate-keeping manager
XXXXX [the Delphi contractor] uses his own RAD Studio Delphi license. I would expect all contractors to have that available as a minimum or I can’t really see how they could be Delphi programmers.
To use a non technical analogy: it’s like us owning a restaurant and hiring a top chef: the chef generally brings his own knives and a bunch of recipes – these are Delphi and the routines and techniques the programmer has learned – but the chef doesn’t usually bring the vegetables and meat to make the meals but if he did you’d probably have to pay him for them – this is like the component sets we choose or need to use.
Sometimes the chef brings in herbs and some beans he grew in his own garden and adds them to the dish and says “I don’t want payment for them” even though he bought the seeds and nurtured them himself – this is like the programmer bringing along some component sets we don’t have but are shareable.